Deploy Pi-Hole and Self-Hosted VPN in the Cloud with Linode
Pi-hole works well for a private server installed on a private network. But it also works for cloud servers. This section of the article walks you through a step-by-step guide on how you can deploy Pi-hole with the help of the Linode Marketplace App keeping security concerns in mind.
NOTE: This article is a work in progress and there may be changes and improvements to security procedures.
$100 – 60 day credit over at Linode: https://linode.com/techhut
Today we are going to be setting up Pi-hole on Linode using their one click installer. But we’re not stopping there. Once we have Pi-hole setup we will set up a recursive DNS server using unbound and then use PiVPN creating our very own Virtual Private Network that we can connect to anywhere in the world.
So in the simplest terms PiVPN will allow us to securely tunnel our network though our Linode and we are going to be doing this with the WireGuard option; however there is OpenVPN is you do prefer. Unbound with allow us to communicate directly with the authoritative name servers of websites instead of needed to use 3rd party names servers like Google or CloudFlare. This may cause slightly slower loading times when first connecting to websites, but the information collected will be cached. Then the cherry on top is Pi-Hole itself witch will filter out ads using their extensive blocked list and give us a wonderful dashboard to manage everything.
ONE CLICK INSTALLER
First, sign in to Linode’s Cloud Manager. From the navigation menu on the left side of the window, select the Marketplace link. This shows the Linode Compute Create with the Marketplace tab being selected already. From the Select App, select the application you want to deploy. In this case, select Pi-hole.
Then fill in all the required Options and any desired Advanced Options. You can take a look at the Configuration Options for details. Then complete the form following this guide given by Linode. Some options may be recommended or limited based on this Linode Marketplace App. For this purpose, supported Linux distros are Debian 11, Ubuntu 20.04 LTS, and you can use any plan type and size.
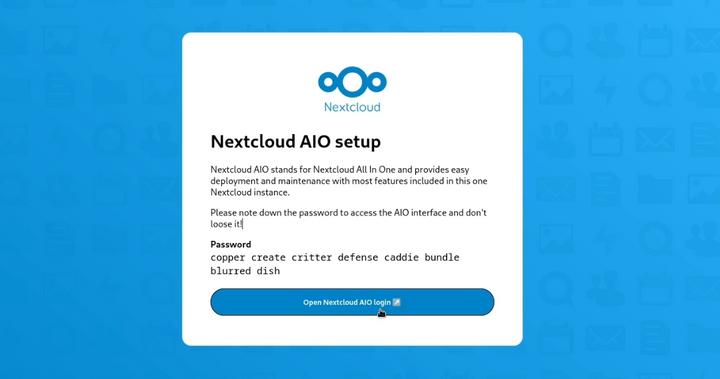
Click on the Create Linode button. After you find the Linode has been provisioned and powered on fully, wait for the software to be installed completely. If Linode is off or restarted, the installation may fail. To check if the Pi-hole installation is successful, open Linode’s Lish console. And then, wait for the login prompt to show up. The installation should take 5-10 minutes to complete. Once the software installation is done, the Pi-hole dashboard should be accessible at the domain that you entered at the beginning of deploying the Pi-hole followed by /admin. Here is an example of what it should look like: http://example.com/admin
In case, you haven’t entered any domain, feel free to use your Compute Instance’s rDNS. This may look like: 123-0-123-0.ip.linodeusercontent.com. Check the Managing IP Addresses guide to find all the information regarding setting and viewing the rDNS value. Once you have landed upon the Pi-hole dashboard, click on the login tab. Then put your Pi-hole user password that was created at the time of your Linode account creation.
Now that you have accessed the Pi-hole dashboard, visit Pi-hole’s official website to learn more about Pi-hole.
BASIC SETUP
sudo apt update && sudo apt upgrade -ysudo hostnamectl set-hostname 45-79-100-49.ip.linodeusercontent.comhostnametimedatectl list-timezonessudo timedatectl set-timezone America/Los_Angelestimedatectl
SETTING UP RECURSIVE DNS
sudo apt install unboundsudo nano /etc/unbound/unbound.conf.d/pi-hole.conf
Part of that configuration was to change the port for unbound from 53 to 5335 so that it won’t interfere with the preexisting Pi-Hole installation. So Pi-Hole will act as the DNS server and forward any requests to unbound on port 5335, then ubound goes out finds the authoritative names severs and forwards that information back to pi_hole in which all the ads will be stripped out.
sudo service unbound restartdig pi-hole.net @127.0.0.1 -p 5335
Login to PiHole and change your Upstream DNS server settings.
Settings > DNS > Custom 1 (IPv4) > 127.0.0.1#5335
This points the upstream DNS to your unbound installation. Uncheck the default Google DNS server options so the only upsteam DNS is your custom IPv4 entry. Save your changes.
VPN SERVICE SETUP
curl -L https://install.pivpn.io | bash
This will guide you though the PiVPN setup. We will do with mostly default settings. Make sure WireGuard is selected as this is what we will be using going forward in this guide. If you prefer or have experience using OpenVPN select that option.
Assuming you selected WireGuard we are going to use our hostname so select DNS Entry and input your hostname from the Pi-Hole dashboard.
WireGuard > DNS Entry
Enable security updates and allow the install script to reboot your system.
CONNECTING TO VPN (MOBILE)
Now we will create a new client and connect to the VPN. For this demonstration I will be connecting with my Google Pixel with the WireGuard Android application.
We will create a new client and call it pixel, you can replace this with whatever works best for you.pivpn -a -n pixel
Next we will generate a QR code to scan via the app.pivpn -qr
There you go! You’re now connected to your very one self hosted VPN with integrated ad blocking! Cool, huh?
Comments ()